- Original:
Securelist P2P Mining Botnet
- Security
The Miner Botnet: Bitcoin Mining Goes Peer-To-Peer
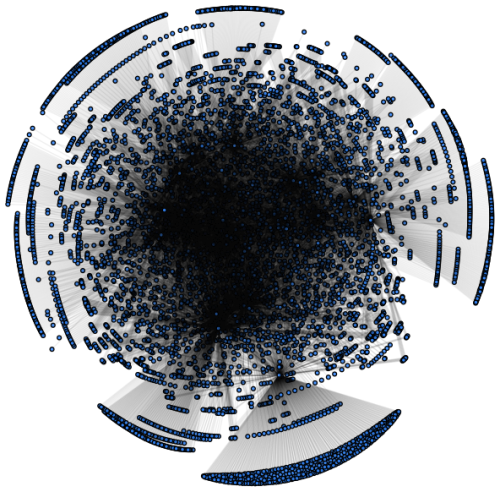
Tillmann Werner, security expert for antivirus software vendor Kaspersky Lab posted his research and analysis of a Bitcoin mining botnet that has become a ”highly interconnected network”.
Botnets deploy and control malware – software that runs on computer systems and, in most instances, were installed without permission from the computer’s owner. The purpose of the malicious software installed through this particular botnet steals computing resources and electricity that performs the mining computations that reward the botnet operator.
This particular botnet operates peer-to-peer meaning infected nodes communicate between each other and not just to the botnet’s command and control servers.
Mr. Werner’s analysis found, in less than a day’s worth of probing, ”a total of almost 38.000 different public IP addresses” participating. He continues: ”taking into account that most machines are behind network address translation or some gateway nowadays, the real number of infected machines can easily be magnitudes bigger”.
Those whose machines are compromised by the botnet may not even realize that something is wrong. The symptoms of an infected computer might include high CPU utilization, skipped frames when game playing or additional network traffic. This software does not appear to inflict general malicious harm to the user and it will likely be most profitable to the botnet operator if the computer user never suspects that the system has been infected.
The protections available are to follow secure computing recommendations which can include running anti-virus software such as Kaspersky Lab’s offerings.